Bank does not need to know where I'm getting my money. Salary, won on horses, won on pokies, my brother and mum helping me out. It's no one's business including ATO. If pushed just say no or lie. ATO has income details. They don't need to cross match with anyone. That's intrusive and going way beyond what's acceptable.
The Aus fed govt needs to know, not the banks.
Its due to then
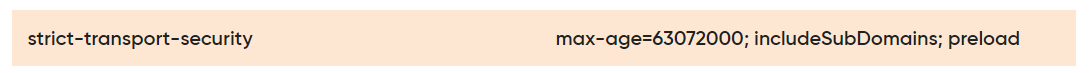
You know that AML/ATT thing that banks "have to do" due to Aus fed govt regulations, talking about time wasting indeed.
45 mins, I spent with one of my banks, name, date of birth, address, employer, employment source, then passport #, medicare #, dl # if you drive, then, they have to check these details off, then contact phone number, they then have to put you on hold, ... then they have to call you back on your mobile phone # you gave.
This bank then has the gall to tell me, I didnt want to cause a fuss, that they would check me with/against data on credit rating agencies, even tho I am not applying for any loans.
Phone and linkT and other scammers have it easy.
Not to mention the "health authority" sms scam.
VFF and QFF and other companies, talk tough, but like Medibank data breach, etc, its so easy for scammers/people who know how to manipulate it, the data is so easy for them to gain.
It should be harder for points to move out of VFF accounts.
VFF should have a code word/words system in place for points transfers out, or points burn.

 www.abc.net.au
www.abc.net.au